Rule to detect vulnerabilites integrating IDS and Vulnerability Scanner - ArcSight User Discussions - ArcSight

Rule to detect vulnerabilites integrating IDS and Vulnerability Scanner - ArcSight User Discussions - ArcSight
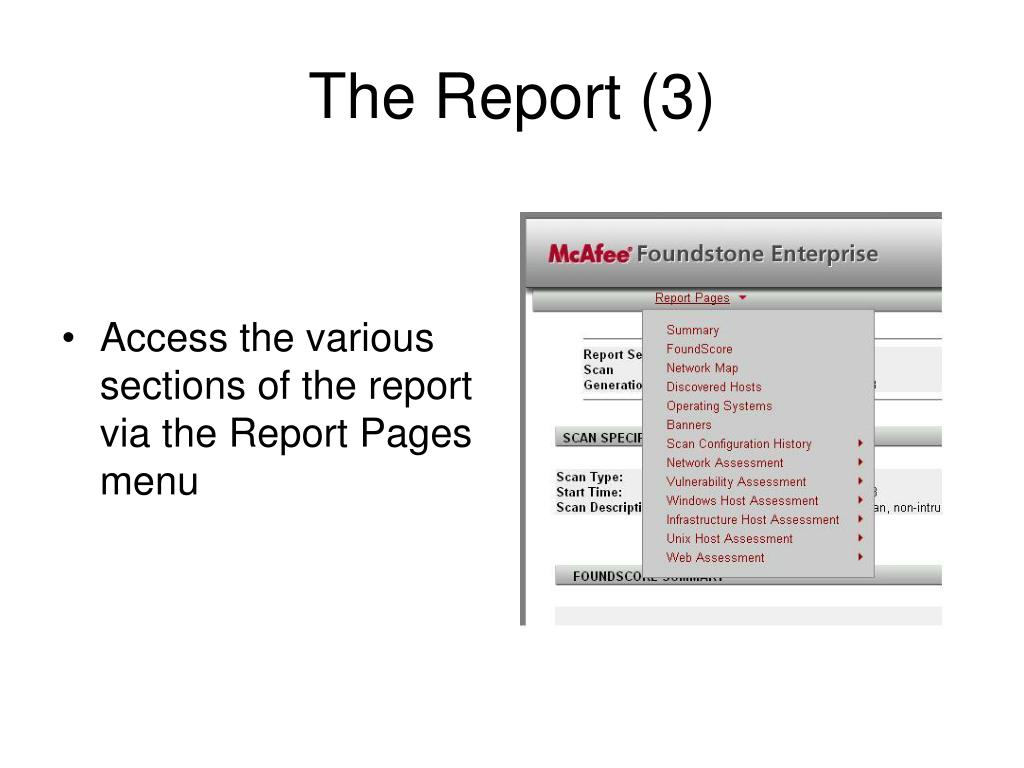
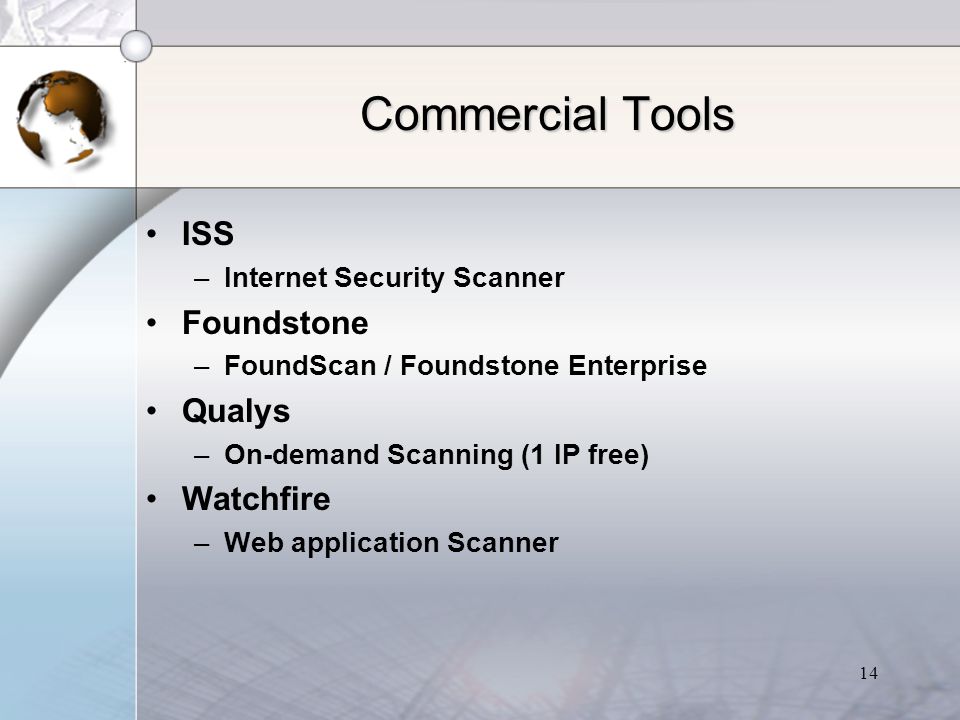
Vulnerability Management for the Real World » Successful Approaches » What is Vulnerability Management? » Challenges to Effective VM » The Problem Contents: - ppt download



![PDF] Vulnerability management tools for COTS software - A comparison | Semantic Scholar PDF] Vulnerability management tools for COTS software - A comparison | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c127551061cde04d7691ea3195bd848b54cfb8c3/4-Table2-1.png)